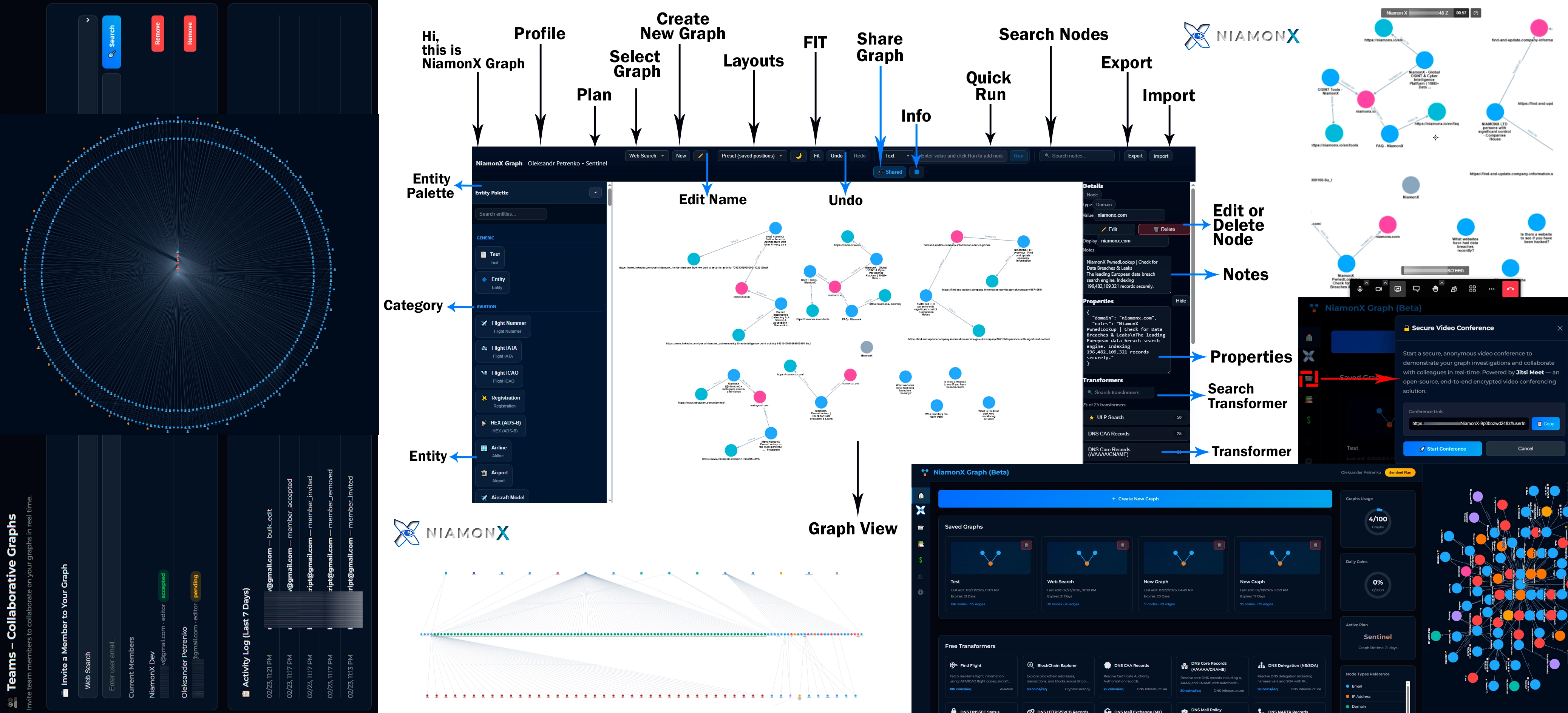
NiamonX Graph is designed for practical, real-world investigations. Its strength is not only in enrichment, but in the way it turns separate technical findings into live visual intelligence. Analysts can start from a single indicator and build a structured map of infrastructure, services, identities, public references, or financial activity without losing context.
The platform is especially effective for cybersecurity teams, OSINT analysts, incident responders, law enforcement, journalists, and digital forensic investigators who need to understand how entities connect, how attack surface expands, and where hidden dependencies or risk clusters exist.
Use Case 1: Domain & Infrastructure Audit
01
Start with a Domain
Enter a domain and immediately pivot into DNS records, nameservers, IP addresses, ASN visibility, SSL/TLS relations, mail authentication records, and internet-facing infrastructure context.
02
Reveal Dependencies
Visualize cloud providers, CDN usage, exposed services, historical infrastructure records, WHOIS context, and related domains to understand the full digital footprint.
03
Document Risk
Mark suspicious hosts, annotate risky nodes, record exposed services, and preserve the operational context of the audit directly inside the graph workspace.
Use Case 2: Phishing & Threat Investigation
Trace the Campaign
Start from a suspicious domain, URL, or IP address and expand into hosting relations, malware verdicts, historical web content, certificate ownership patterns, and other linked indicators.
Identify Overlap
Find shared infrastructure, reused services, hidden third-party dependencies, related domains, and historic pivots that may connect one phishing asset to a broader campaign.
Support Response
Provide a graph-based view that helps SOC teams, blue teams, and incident responders communicate scope, exposure, and priority more clearly.
Use Case 3: Blockchain & Financial Tracing
NiamonX Graph supports blockchain-centric analysis where investigators need to understand relationships between addresses, transactions, services, sanctions signals, and potentially risky wallet behavior. Instead of reading isolated transaction outputs, analysts can map movement and context visually.
- Explore Bitcoin, Ethereum, Litecoin, and Dogecoin-related entities
- Follow wallet-to-transaction and transaction-to-wallet pivots
- Overlay sanctions checks and contextual intelligence where available
- Preserve relationships and notes for financial investigation workflows
Use Case 4: OSINT & Public Research
For investigative journalists, researchers, and open-source intelligence teams, NiamonX Graph can combine public web results, news references, places, maps, videos, images, documents, and related technical indicators into one coherent visual research environment.
- Connect mentions across public sources
- Track related domains, services, and identities
- Review historical snapshots through the Wayback Machine
- Document investigative hypotheses with structured notes
Why a Graph-First Workflow Changes Everything
Traditional workflows force teams to jump between tabs, export fragments into spreadsheets, and manually reconstruct logic. NiamonX Graph replaces that with a live intelligence map where every pivot, enrichment, note, and relation stays visible and actionable.
01
See More
Understand the broader context of an indicator through connected relationships rather than isolated results.
02
Move Faster
Reduce pivot time and correlation effort across cyber investigations, infrastructure audits, and public intelligence workflows.
03
Keep Context
Retain analyst reasoning, evidence paths, and operational notes directly within the same visual environment.
Connected Ecosystem for Deeper Intelligence
NiamonX Graph becomes even more powerful as part of the wider NiamonX ecosystem. Infrastructure findings can connect to Internet Surface visibility, technical pivots can be extended with transformers, and research workflows can be deepened through official documentation and internal knowledge paths.
FAQ about Investigation Workflows
Real-world use cases for infrastructure audits, phishing investigations, blockchain tracing, and OSINT research.
SOC teams, threat intelligence analysts, incident response teams, pentesters, digital forensic investigators, journalists, blockchain researchers, and law enforcement teams can all benefit from graph-based investigative workflows.
Yes. Domain and infrastructure auditing is one of the strongest use cases. Analysts can pivot from one domain into DNS, IP, ASN, certificates, services, historical records, and broader digital infrastructure relationships.
Yes. Investigators can map suspicious domains, linked infrastructure, SSL/TLS relations, historical content, reputation signals, and connected indicators in a visual way that improves campaign analysis and response clarity.
The platform allows teams to keep graph relations, notes, risk flags, enrichment pivots, and visual evidence paths inside one live workspace instead of scattering them across separate tools and documents.
